How Emergency Notification Systems Work and Why Cloud-Based Platforms Matter
Why Emergency Notification Systems Matter More Than Ever
Organizations today operate in environments that are more complex and interconnected than ever before. Many institutions now span multiple facilities, campuses, or geographic regions. Employees may work remotely or move between locations throughout the day. Visitors, contractors, and temporary personnel may also enter facilities regularly.
At the same time, operations increasingly rely on interconnected digital infrastructure. Networks, communications systems, building controls, and security technologies all play a role in how organizations function. When an unexpected event occurs, the ability to communicate quickly across this environment becomes critical.
In the past, emergency communication often relied on simple methods such as phone trees, radio calls, or overhead announcements. These approaches worked when organizations operated within a single building or when communication needs were relatively limited. Today, however, organizations must communicate across large facilities, outdoor spaces, and distributed teams.
Modern emergency notification systems help solve this challenge. These platforms allow organizations to distribute alerts rapidly across multiple communication channels so that people receive instructions as quickly as possible. Instead of relying on one person to manually contact others, automated systems coordinate communication across devices, buildings, and communication technologies.
Organizations in many industries rely on this capability. Schools must communicate quickly with staff and students. Healthcare facilities must notify teams across large medical campuses. Manufacturing facilities must alert workers across production floors and warehouses. Municipal governments must coordinate responses across departments and facilities.
In all of these environments, communication directly affects how quickly people can respond to changing conditions. Delayed or unclear messages can lead to confusion, slow responses, and operational disruptions.
Understanding how emergency notification systems work helps organizations evaluate whether their current communication infrastructure can support rapid, reliable alerts when situations evolve quickly.
To explore available solutions designed for these environments, organizations can review modern emergency notification systems that support coordinated communication across facilities.
What Is an Emergency Notification System? A Modern Definition
An emergency notification system is a technology platform designed to distribute urgent messages and instructions during critical situations. The system helps organizations quickly notify employees, occupants, or visitors when a situation requires immediate attention or action.
At a basic level, the system sends alerts. However, modern platforms go far beyond simple messaging. They function as coordinated communication systems that connect multiple technologies, workflows, and operational processes.
When an incident occurs, the system can automatically trigger a sequence of communication actions. These actions may include voice announcements across a facility, text alerts to mobile devices, visual warnings through digital displays, and notifications sent to administrators or response teams.
The goal of these systems is not only to send messages but also to guide people toward appropriate responses. For example, alerts may instruct individuals to evacuate, shelter in place, avoid certain areas, or follow specific safety procedures.
Many organizations mistakenly assume that mass messaging tools provide the same functionality as emergency notification systems. While messaging platforms can distribute alerts, they often lack the infrastructure integration and automated workflows required during real emergencies.
True emergency communication platforms coordinate multiple communication channels and technologies. They also allow organizations to create predefined response scenarios so that alerts can be triggered quickly without requiring complex manual steps.
For example, an organization may configure response workflows for events such as severe weather warnings, security incidents, or operational disruptions. When one of these events occurs, the system can immediately activate the appropriate communication sequence.
These platforms also support communication across multiple groups or locations. Messages can be directed to specific departments, facilities, or personnel depending on the nature of the incident.
By coordinating communication across people, devices, and infrastructure, emergency notification systems help organizations deliver clear instructions during moments when rapid response is essential.
How Emergency Notification Systems Work Behind the Scenes
To fully understand how emergency notification systems work, it is helpful to examine the internal processes that occur when an alert is triggered. Modern platforms operate through structured communication workflows designed to deliver accurate information quickly.

Although the exact configuration may vary by organization, most systems follow a similar sequence of steps.
Incident Detection or Alert Initiation
The process begins when an incident is identified. This can occur through manual or automated triggers.
Manual triggers allow authorized personnel to initiate alerts from phones, control panels, software dashboards, or emergency buttons placed throughout a facility. These tools allow staff members to activate notifications quickly when they observe a situation that requires immediate communication.
Automated triggers can also initiate alerts. Some emergency notification systems integrate with building technologies such as access control systems, video surveillance platforms, fire alarms, or environmental sensors. When these systems detect specific conditions, they can automatically initiate communication workflows.
For example, a security system may detect unauthorized access after hours and trigger notifications to security personnel.
Message Creation and Scenario Selection
Once an alert is triggered, the system generates a message or selects a predefined communication scenario. Organizations typically create templates for different types of incidents so that instructions remain consistent and easy to understand.
These templates may include both written and spoken messages. For example, a severe weather alert might include an automated announcement instructing people to move to interior areas of a building.
Using predefined templates reduces delays and ensures that communication remains clear even when incidents occur unexpectedly.
Communication Channel Routing
After the message is generated, the system determines which communication channels should deliver the alert. Routing rules allow organizations to send messages through multiple technologies simultaneously.
Different channels may be used depending on the type of alert or the location of recipients. For example, an organization may send a message through paging systems within a building while also sending mobile alerts to employees who may be off-site.
Message Distribution
Once routing decisions are made, the platform distributes alerts across all selected channels. This may include overhead announcements, mobile messages, desktop alerts, and visual indicators throughout a facility.
Simultaneous communication across multiple channels increases the likelihood that individuals receive and understand the message quickly.
Confirmation and Escalation
Some systems also track message delivery or acknowledgment. If a message is not received or acknowledged within a specific time frame, the system may escalate the alert by sending it to additional recipients or using additional communication channels.
This escalation process helps ensure that important alerts are not overlooked.
Overall, emergency notification systems function as coordinated communication engines. Rather than simply broadcasting messages, they manage workflows that ensure the right information reaches the right people at the right time.
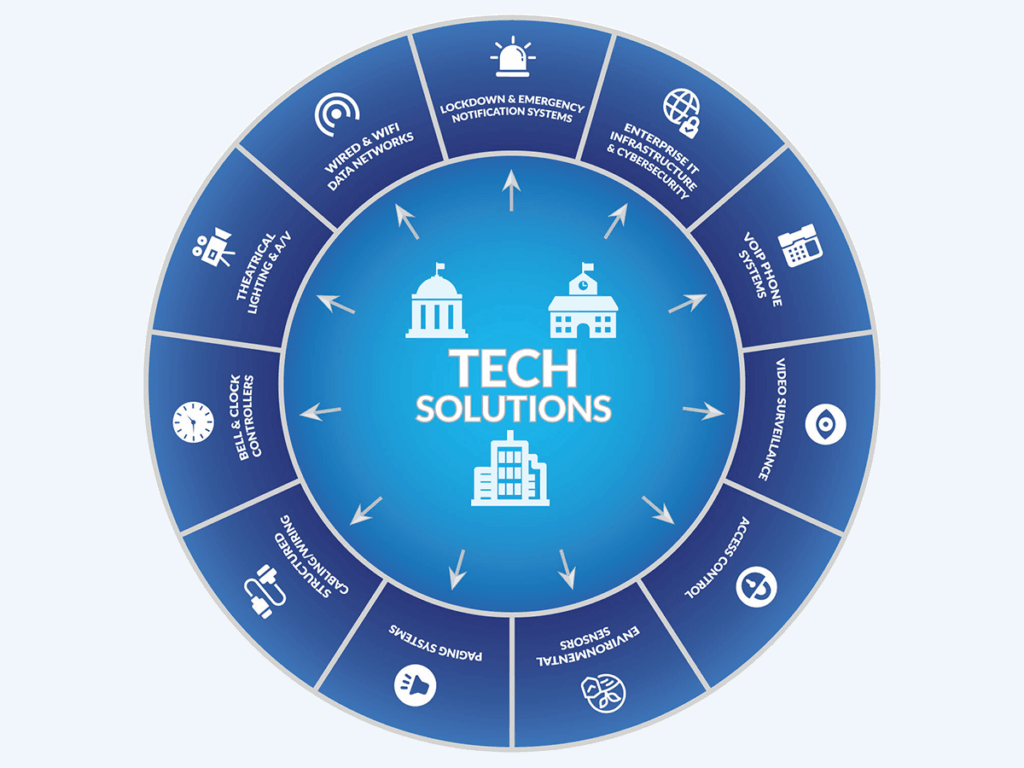
The Communication Channels That Power Emergency Alerts
Effective emergency communication requires multiple communication channels working together. No single communication method can reliably reach everyone in every situation.
For example, mobile alerts may not reach individuals who do not have their phones nearby. Overhead announcements may not be audible in noisy areas or outdoor spaces. Visual alerts may be missed if individuals are not facing digital displays.
Modern emergency notification systems address this challenge by coordinating several communication technologies.
Voice Announcements and Paging Systems
Public address systems remain one of the fastest ways to deliver instructions across large facilities. Paging announcements can reach large groups of people simultaneously and are especially useful for communicating urgent instructions.
SMS and Mobile Notifications
Mobile alerts allow organizations to reach individuals who are not near building communication systems. These alerts can provide instructions, updates, or safety information through text messages or mobile applications.
Desktop and Digital Alerts
Pop-up alerts on computers or digital signage can reinforce verbal announcements and ensure that employees working at computers receive notifications immediately.
Visual Warning Systems
LED beacons, message boards, and digital displays provide visual indicators of emergencies. These alerts are especially useful in environments where loud machinery or other noise may interfere with audible announcements.
Telephony and VoIP Systems
Modern phone systems can also play a role in emergency communication. Integrated communication infrastructure, such as VoIP alerting and communications, can deliver automated calls, announcements, and alerts across internal networks.
When these channels operate together, organizations achieve broader coverage and greater reliability. If one communication method fails or is unavailable, other channels can still deliver the message.
What Determines Emergency Notification System Reliability
Reliability is one of the most important characteristics of an emergency notification system. During critical situations, organizations must be confident that alerts will reach the intended recipients without delays or technical failures.
Several factors influence the reliability of these systems.
Network Infrastructure
Emergency communication platforms rely on network connectivity to distribute messages across devices and communication systems. If the underlying network cannot support high traffic volumes or rapid message distribution, communication delays may occur.
Redundant Communication Paths
Reliable systems include redundant infrastructure and backup communication paths. If one component fails, other systems can continue delivering alerts without interruption.
System Scalability
Large organizations may need to send alerts to thousands of recipients simultaneously. Notification platforms must be capable of scaling to support these high-demand situations.
Governance and Operational Procedures
Technology alone cannot guarantee reliable communication. Organizations must establish clear policies that define how alerts are triggered, who is authorized to initiate them, and how communication workflows operate.
Regular Testing and Maintenance
Routine testing ensures that communication channels, devices, and integrations continue functioning as expected.
A strong technological foundation plays a key role in these capabilities. A reliable security infrastructure backbone supports the network performance and system integration required for effective emergency communication.
Common Failure Points in Emergency Communication Systems
Despite the availability of advanced communication technologies, many organizations still experience communication gaps during emergencies. These gaps often occur because systems were designed without considering the full complexity of modern facilities.
One common issue involves relying on a single communication channel. Systems that depend only on mobile applications or text alerts may fail if network connectivity is limited or if individuals do not have access to their phones.
Another challenge involves outdated on-premises systems that cannot scale to support modern communication demands. Legacy infrastructure may lack integration capabilities or fail to support multiple communication channels simultaneously.
Coverage gaps are another frequent problem. Outdoor areas, parking lots, athletic fields, or remote facility spaces may not receive alerts if communication systems were designed primarily for interior spaces.
In some cases, communication tools operate independently rather than as part of an integrated system. When security technologies, phone systems, and notification platforms do not work together, organizations may experience delays or confusion when responding to incidents.
Organizations can reduce these risks by implementing integrated platforms that coordinate communication across multiple technologies and locations.
The Role of Cybersecurity in Emergency Notification Delivery
Emergency communication systems must be trusted by the people who rely on them. When individuals receive an alert, they must believe that the message is legitimate and accurate.
Cybersecurity plays a crucial role in maintaining that trust.
Modern notification platforms include security protections that prevent unauthorized access and protect sensitive information. These protections may include user authentication, access controls, encrypted communication channels, and activity monitoring.
Without these safeguards, communication systems could be vulnerable to unauthorized alerts or malicious activity.
Organizations increasingly focus on protecting their communication infrastructure through cyber-secured emergency communications. These protections ensure that emergency messages remain reliable and that communication systems continue operating during cyber incidents.
What Is a Cloud-Based Emergency Notification System?
A cloud-based emergency notification system operates on hosted infrastructure rather than relying entirely on servers located within a single facility.
Traditional on-premises systems depend on local hardware that must be maintained and updated within each building or campus. While these systems can provide communication capabilities, they often face limitations in scalability, redundancy, and remote management.
Cloud-based platforms address these limitations by hosting the notification platform within secure cloud infrastructure.
This architecture provides several advantages.
Organizations can manage alerts from a centralized platform that connects multiple facilities. Administrators can coordinate communication across buildings or regions without needing separate systems for each location.
Cloud infrastructure also supports greater redundancy. Because the platform operates across distributed data centers, the system can continue functioning even if one location experiences technical issues.
Another advantage is scalability. Cloud platforms can handle large communication volumes during emergencies when thousands of alerts may need to be delivered simultaneously.
Remote management capabilities also allow administrators to trigger alerts from secure devices even when they are not physically present at a facility.
Cloud architecture forms the foundation for modern communication solutions such as the LENS IP platform, which supports cloud-based emergency communications across complex environments.
Modern Cloud Platforms vs. Legacy Systems
Legacy emergency communication systems were often designed to serve a single facility with limited communication channels. While these systems provided basic alerting capabilities, they were not designed to support today’s distributed organizations.
Cloud-based platforms provide greater flexibility and resilience. These systems allow organizations to expand communication capabilities across additional buildings, campuses, or departments without extensive infrastructure changes.
Cloud platforms also integrate more easily with other technologies such as phone systems, security platforms, and digital signage. These integrations allow organizations to coordinate communication across multiple systems during emergencies.
Another advantage involves system updates and maintenance. Cloud platforms can receive updates and security improvements automatically, reducing the need for complex on-site upgrades.
Modern solutions such as Eastern DataComm’s emergency notification systems and the LENS IP platform are designed to support the communication needs of complex organizations.
Where LENS IP Fits in the Emergency Communication Ecosystem
Within the broader emergency communication ecosystem, platforms such as LENS IP serve as the operational layer that coordinates communication workflows and technologies.
Instead of operating as a standalone messaging tool, the platform integrates with existing infrastructure such as paging systems, VoIP networks, and visual alert systems. This integration allows organizations to activate coordinated communication responses that reach multiple channels simultaneously.
Systems designed by experienced integrators also account for the real-world challenges organizations face. These challenges include network performance, building layouts, and the need to communicate across indoor and outdoor spaces.
Eastern DataComm’s approach reflects decades of security integration expertise, helping organizations implement communication systems that function reliably in real facilities.
Testing Emergency Notification Systems Before an Incident Occurs
Testing is essential for ensuring that emergency notification systems remain reliable over time. Communication technologies must be verified regularly to ensure that alerts reach the intended recipients and that systems continue functioning properly.
Testing activities may include verifying paging announcements, confirming mobile message delivery, and testing visual alert systems across different areas of a facility.
Organizations may also conduct communication drills that simulate real emergency scenarios. These exercises allow staff members to practice activating alerts and responding to notifications.
Testing helps organizations identify coverage gaps or communication delays before an actual emergency occurs. Addressing these issues proactively can significantly improve response times during real incidents.
Organizations interested in evaluating their current systems can request a consultation or schedule a demo to explore opportunities for improving their emergency communication infrastructure.
Building Emergency Communication Systems You Can Rely On
Reliable emergency communication requires more than a single technology. It requires a coordinated system that connects infrastructure, communication channels, operational workflows, and cybersecurity protections.
Understanding how emergency notification systems work helps organizations evaluate whether their current systems can deliver alerts quickly and clearly during critical situations.
Modern cloud-based platforms provide the scalability, resilience, and integration capabilities needed to support complex facilities and distributed teams.
Organizations that invest in resilient communication infrastructure are better prepared to respond quickly, coordinate effectively, and maintain operational continuity when unexpected events occur.
To explore how modern communication platforms can strengthen your organization’s safety and communication capabilities, learn more about emergency notification systems or schedule a consultation.